Overcoming Censorship
Overview
Online censorship has ramped up significantly in the past few years. We've all seen it. For instance:
-
Seemingly innocuous social media posts getting removed for reasons that make no sense, or for no reason at all
-
Veiled and not-so-veiled threats about what you are allowed to say online without fear of losing your job, getting kicked out of school, or even being physically assaulted
-
Ridiculous, unbelievable "official" versions of events being amplified by fake accounts and clickbait-driven media outlets
-
Personal experiences being mocked or dismissed as hoaxes or "conspiracy theories" in spite of supporting evidence (i.e. gaslighting)
Censorship comes in many flavors, but it always ends in either forced removal of content, or intimidation into silence. Thankfully, overcoming tech censorship is surpsisingly easy, with the right tools and knowledge of how to use them.
Understanding the technology and censorship landscape
Back in the 1990's, there was an internet rumor that continually made the rounds on email and personal websites. It said that the government had a computer system called ECHELON that was scanning everyone's email looking for specific words and phrases so that they could identify dissidents, political enemies, or whatever. What could be done against this massive spy effort?
The email, which contained an ever-growing list of the ECHELON trigger words, proposed an ingenious solution: purposely flood the system by forwarding the email to everyone you know. It wouldn't crash the system, but it would create enough false positives to hamper the system's utility and make it hard to differentiate the signal from the noise.
(Incidentally, it turns out ECHELON is real, and was operating not unlike the way the email described it. It's funny how the more goofy sounding conspiracy theories occassionally turn out to be true.)
How large-scale censorship is accomplished
What's this got to do with censorship?
Big surprise alert: most censorship is semi-automated. We've all heard of the legendary algorithms that suppress search results, throw your grandpa's forwarded emails into the spam bucket, deboost your posts, or simply shadowban your social account altogether. Without getting into the technical details of how they work, many of these algorithms are continually tuned by humans to ensure they continue to do their job in spite of attemps to get around them. This is why it often feels like a person is vetting your posts. But make no mistake, even with fine tuning, these algorithms have severe weaknesses that make them trivial to circumvent.
The weaknesses of automated censorship
Censorship systems are always relearning what's normal based on the totality of what people are posting. Let's go back to the ECHELON email for a moment. The idea of flooding the system with noise to make it less effective might seem silly, but it's theoretically sound. Pushing down the signal-to-noise ratio is going to cause problems in any system because you're disturbing a feedback loop. You're witnessing this effect in social media right now. So many people are posting about messenger RNA pharmaceuticals, cardiac issues, "aye-vur-meq-tin", etc. that these posts no longer stand out as unique or suspicious. When such posts were less common, it was easy to have an algorithm flag them for human review. But now it's no longer practical for a human to review all these posts, so the censors have to tighten up the algorithm to detect and remove the forbidden posts. When that happens, you get more false positives, and people who normally don't post anything controversial suddenly find their completely innocent posts being blocked.
This is where the game changes, and we're rounding this corner right now. People who heretofore didn't care about censorship or thought it was overblown are now finding themselves victims of it. Whereas they used to ignore the issue, some are now becoming vocal about their experiences (for example, of grandma's account getting suspended because she innocently shared a funny meme). More to the point, they're sharing these stories, thus further upsetting the algorithm. It's the slippery slope of automated censorship.
If your goal is to disseminate information, the algorithm is your enemy, and you must avoid it like the (other) plague.
Your accounts are about to be deleted
Before we get started, a warning is in order. Don't use any social media platform, web host, or email provider as your onnly storage bin for your contacts or content. You could lose it at anytime and without warning.
Get alternate contact information for everyone in your audience, whether it's your friends list, followers, contacts list, whatever. You never know when you'll lose access to that information, so get it right now, before you post anything else. And make a backup of your posts. I can't emphasize this enough.
The social media site Parler made a huge mistake by keeping everything on one cloud platform with no backup. If you were using Parler around the time of the January 6 protest/guided tour, you know what happened. They were down for over a month and their CEO got fired over it.
Around the same time, MailChimp abruptly canned accounts that were sending emails calling for analysis of the 2020 Presidential election. Those people who didn't have a current backup lost access to their email lists.
Do you have emails or phone numbers for the people you talk to? Yes? Good, because phone numbers are useful for more than just phone calls and SMS text messages.
Telegram and Signal
Telegram and Signal are apps that let you securely chat with your contacts privately one-on-one or in a group using voice, video, or text.
Telegram does private chat, group chat, and read-only channels that you can use to blast messages to subscribers. It supports voice and video chat as well. They have millions of users and many people and groups that are active on other social sites also cross-post to Telegram. You do have to provide a phone number to sign up.
Signal is more geared toward private, secure chats, similar to SMS. It also requires a phone number.
Check them both out. The idea here is to have options and alternative channels of communication, not to become dependent on just one or the other.
Stop using Gmail
Please, please, PLEASE stop using Gmail, and tell your friends to stop using it, too. Use Fastmail, Protonmail, or something else.
Gmail is infamous for putting your most interesting emails into the spam folder. And you already knew their algorithms are scanning your emails to target you for advertising and who-knows-what-else!
Go ahead and throw Yahoo! mail in there also. It's just as bad.
Strategies for Avoiding Censorship
Whatever you do, don't trigger the algorithm! But how do you do that if you don't know what the algo is looking for? The trick is to make your content blend in with everyone else's. Hide the signal in the noise.
Code words and euphemisns
The most natural and easiest way to discuss a touchy subject without tripping any alarms is to use code words and euphemisms. Read the following examples and see if you can figure out the message based on the context:
"Since my appointment, my HR has been elevated and my doc says I have some sort of itis"
"Aunt Talatha was a little overweight, but she was still healthy. Nobody can explain why she passed so soon after receiving 'protection'"
"Started having symptoms 3 days ago. Did a televisit and got some medicine supposedly for animals that neigh. Feel soo much better now."
You probably understood each message perfectly just by reading between the lines. It took a little thought and effort to avoid using certain words, and the sentences are longer than they could've been, but nothing in them would raise any red flags.
This approach works only if the people reading it have sufficient context. Speaking of using euphemism in music lyrics, Brady Goodwin, Jr. put it this way:
...we can speak to those who are 'in the know' without unnecessarily informing those who do not need to know. To accomplish this, artists must become acquainted with and skilled in the art of euphemism—saying it without saying it.
Hence, this isn't a good strategy for communicating new information. For that, you'll have to use another approach.
Crazy, phonetic spellings for troublesome words
For technical topics, you're going to have to use technical words. And algorithms love technical words because they have a very well defined meaning. Take the following example which would likely trigger something:
Comirnaty induces antibodies against the spike S1 protein antigen, whereas natural infection generates antibodies against multiple viral proteins.
Even if you dumb down the language, you'll still have some potentially problematic technical terms that are hard to get rid of:
The you-know-what gives you antibodies against only one part of the virus, but natural infection creates antibodies against many of its parts.
The challenge with technical content is that you can't get rid of the technical terms without losing the impact, and possibly the meaning. One way around this—and it's not perfect—is to use shorthand and phonetic spellings that look nothing like the word, but sound like it when spoken.
The v. induces anty botties against the S1 Pro, but nat. infection creates anty botties against many of its parts.
Does that look stupid? Yes. Will it fly under the algorithm's radar? Also yes. Algorithms are terrible at understanding context because algorithms don't understand anything. They're just computer programs.
Notice I used "S1 Pro" instead of "S1 protein". The latter has one very specific meaning, whereas "S1 Pro" can refer to speakers, auto parts, viruses, or a number of other different things. Imagine the reaction if a rigid algorithm flagged every audio enthusiast bragging about their new "S1 Pro" because it might be "misinformation!"
Memes and other images
Memes are essentially visual metaphors. They're extremely powerful and, if done right, nearly impossible for an algorithm to detect because algorithms aren't people and can't understand metaphor (this is why your computer doesn't laugh when you tell it a hilarious joke).
The meme below features the rapper Drake comparing... well, it speaks for itself.
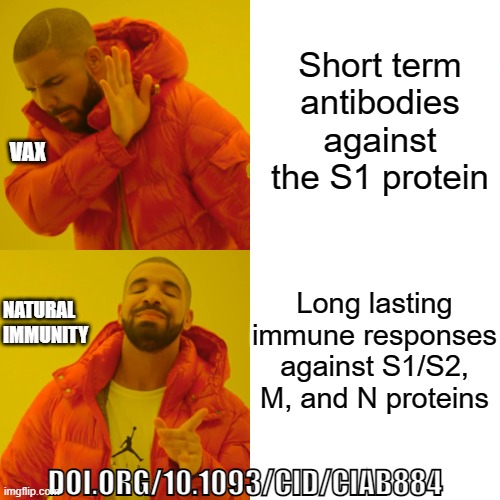
Memes like this are ridiculously easy to create. https://imgflip.com/memegenerator is my favorite but there are others. Pick a meme, type some text, download it, and share away.
Keep in mind that algorithms can easily read any text you put into an image, however, because it's more computationally intensive to scan every single image anyone shares or uploads, there's usually a delay before the algorithm deciphers your awesome meme and flags it. To avoid this, apply the preceding circumvention tips to any text your put into your memes.
Or...
Turing-safe images
You know how a site will sometimes ask you to look at a mangled picture of some letters or numbers and type them in a box to prove you're not a robot? This is called a Turing test, and it's designed to be difficult for computers to solve but easy for humans. Below is an image I created using https://fakecaptcha.com:

I ran this through multiple optical character recognition (OCR) tools and none of them could recognize the first word. Some couldn't even recognize any of the words. N.B., this is of limited usefulness because the text is intentionally difficult to read.
Try combining a Turing-safe image with a meme and you'll be unstoppable.
Archive stuff before it gets dirty deleted or memory-holed
Have you ever heard that stuff you put on the internet lives forever? It's not true.
About 15 years ago I was doing work for an accounting firm owned by an older gentleman who made it a point to turn off the internet router every day before leaving the office. One day as we were discussing this peculiar habit, the conversation took an interesting turn. He pulled an old book off a nearby shelf and pointed out that unlike information on the internet, once a book was published, no one could go back in and change it.
Indeed.
Even medical journals and official government sites have removed published papers because they were radioactive. That's why when you find something interesting that's apt to get edited or removed, take a moment to capture an archive of it. Archive.today is my go-to because they won't delete archived pages just because someone requests it. Contrast this with Archive.org which blacklists certain sites and even removes them (perhaps for the right price).
Take screenshots, or use the Print to/Save as PDF or Web capture functions in your browser to keep local copies of interesting things you find.
Share files and images with others using sites like https://anonymshare.com, https://imgbb.com, or https://anonfiles.com.
Have separate public and private accounts
Just as you should have a backup of your contacts and posts, you may want to have multiple accounts for each service you use. Your accounts should not be in any way linked. Don't use the same name, email address, or phone number for multiple accounts, and don't allow the accounts to interact with each other in any way (e.g. "like, follow," comment, etc.)
Public
One account can be public and highly visible, used for blasting info to anyone who will listen.
Your public posts should appear "safe" and be rational and level-headed. Avoid hysterics and emotional manipulation techniques like the clickbait media uses. For example, state "x deaths caused by lung cancer" instead of "Heartless big tobacco sacrificed x lives for profit!" You get the picture. Use your public presence to slyly invite like-minded people into your inner circle. For example, on my Contact page you can find my email address and a link to my Telegram.
Private
The other account should be private, low-key, and not obviously tied to your public persona. The most controversial and sensitive posts should go only to a select group that you trust not to report you. You still must avoid triggering the algorithms, but you're free to be more blunt if you know no one is going to turn you in to the stasi.
A word of wisdom: Save the unbridled venting for your secret diary. I cringe when I see people giving full vent to their anger, rage, and frustration online. This is a fool's errand. Even in your private, inner circle, be circumspect about what you say. Assume that someone outside of your circle is going to see it, because they eventually will. Judgment day, remember?
You've been censored. Now what?
Remember that false positives are inevitable, so even if you do everything right, one of your posts is going to get flagged. Let's talk about the proper way to respond.
Think carefully before you react, and resist the urge to immediately announce that you've been censored. There's a saying that if you throw a rock at a pack of dogs, the one that yelps is the one you hit. When you publicly start complaining about how you were censored, you actually may unwittingly encourage others to start censoring themselves out of fear. Silence is golden.
Vague warning
Some sites take a behavior-modification approach by giving you some vague warning that your content violated some set of rules that's 30 pages long, but stop short of telling you precisely how you violated the rule. Or they claim you violated a specific rule that you did not actually violate.
This is a lazy mind game and the primary goal is to get you to censor yourself. The secondary goal is to get you to tell others that you've had your hand slapped so they'll get spooked and fall in line. It's a trap. Just ignore the warning, say nothing about it, and move on.
Post hidden or deleted
If your post was hidden or deleted, post it again with modifications. Try to reword the entire thing, if you can, so that it isn't detected as a duplicate. Also, if the original post was simply hidden and not deleted, delete it before reposting.
Content removal is a game of whack-a-mole. Having content detected and deleted is usually just because your number came up. Roll again and you'll probably win.
Account suspended or banned
Once this happens, your account has a black mark on it indefinitely. The best option is to delete the account, wait a while, and create a new one. Social platforms are wise to this, so use a different email, name, phone number, and preferably IP address when signing up.
Shadowbans
Shadowbans are quite possibly the most effective way to remove inconvenient content from a platform. When shadowbanned, your content is visible to you but hidden to others—either by being invisible or just buried beneath layers of "click here to see more."
Having multiple accounts makes it easy to detect if you're being shadowbanned. If you suspect one account is being shadowbanned, for example, just log in with an alternate account and see if you can see the content. If not, you're shadowbanned. Dealing with a shadowban is the same procedure as dealing with a normal ban: delete the account and start over.
Censorship-resistant platforms
If you're not keen on flying under the radar of the all-seeing algorithm, you may want to move to friendlier pastures where you're free to be less reticent.
The following are various chat and publishing platforms that have a decent track record of not being heavy handed. If you have any to add, let me know.
Long-form publishing
Substack is designed for long-form content such as articles or blogs. I follow a few different blogs hosted there, and have detected no signs of censorship thus far. Of course, keep a backup of any posts you don't want to lose.
Social media
You're probably already aware of these, nevertheless, here they are in no particular order:
Parler https://parler.com and Gettr https://gettr.com are for short-form posts, like that awful site that starts with a T
Gab https://gab.com and Mewe https://mewe.com are fashioned after Fakebook, but aren't funded by the CIA (as far as you know).
Conclusion
They can't censor what they can't control. As long as you have access to your contacts and content, you can find a way to distribute information.
In addition to flying under the radar of the dumb-but-smart algorithms, there are other ways to circumvent censorship that are a bit more technical and require some time and effort to implement, such as:
-
Virtual private networks (VPNs)
-
Throwaway email addresses
-
Tracker blocking
And yes, you hear commercials for these kinds of services making it sound like you can just push a button, and suddenly you're anonymous or invisible. Unfortunately, it's not that simple. An algorithm may be aware of these tools and become more touchy when it detects them, thinking that they indicate a bot. To avoid triggering the algorithms, you want to appear as normal as possible. I therefore recommend keeping it simple and adding the aforementioned tools one at a time, learning as you go.